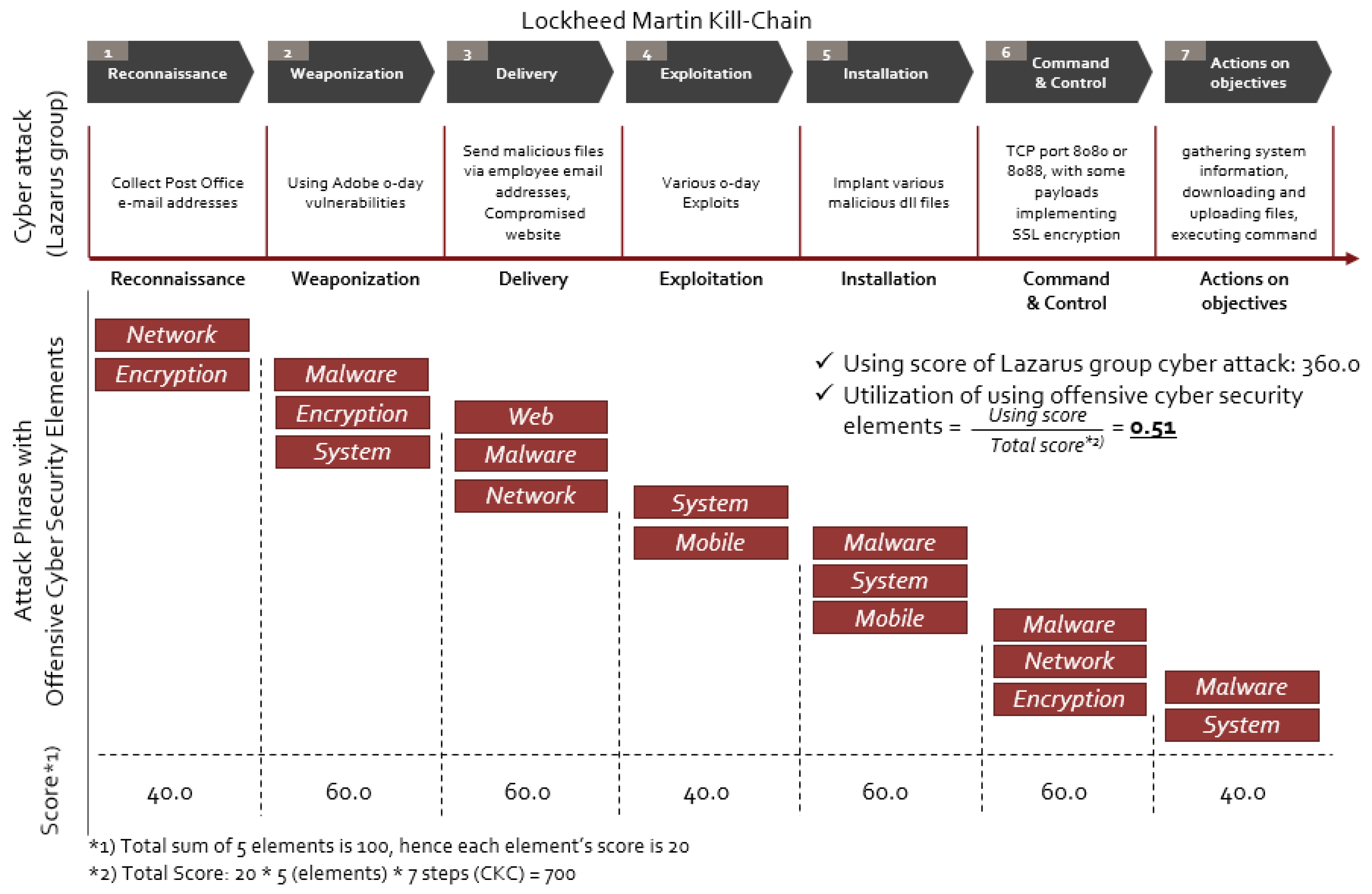
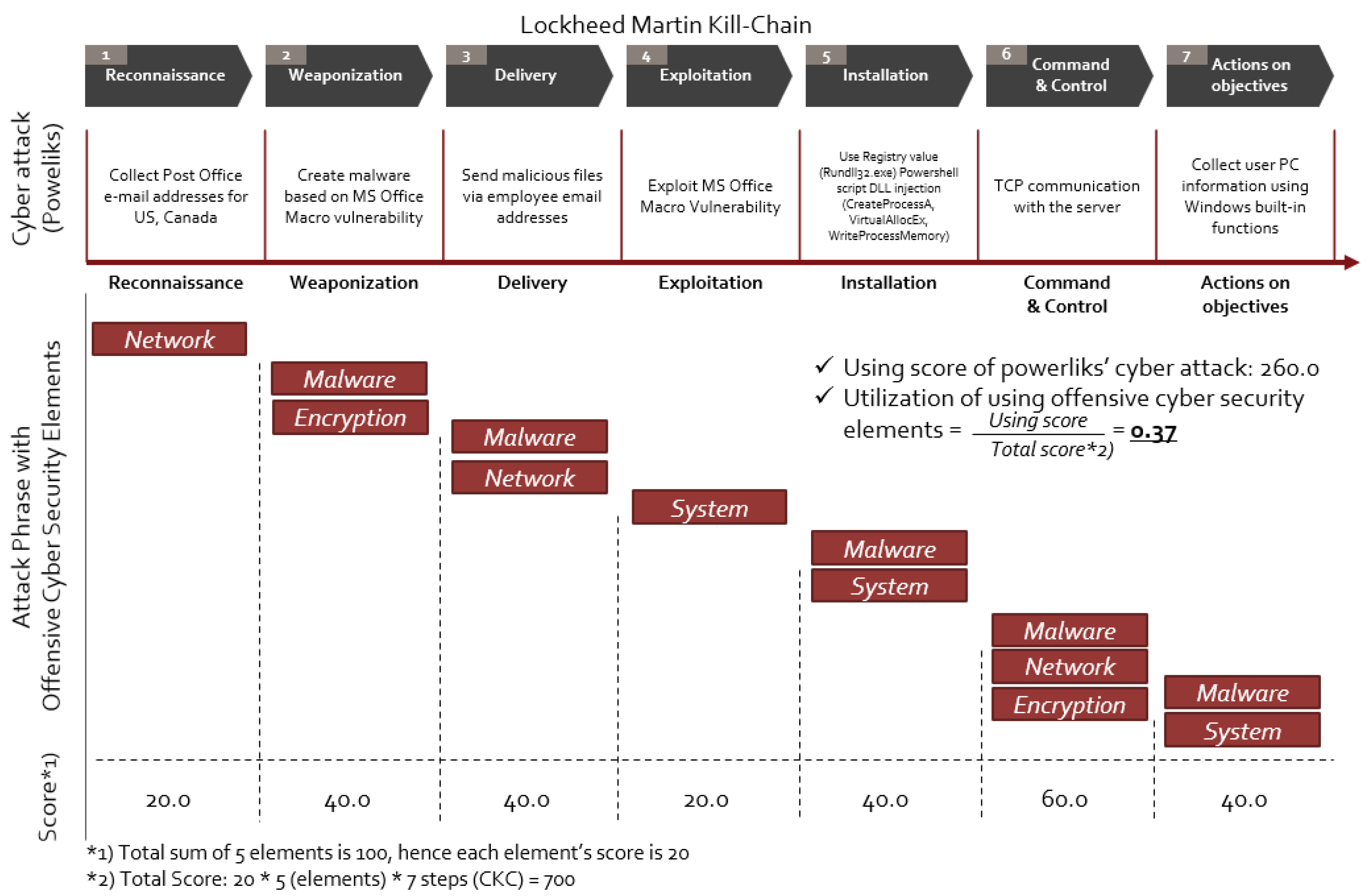
Applied Sciences | Free Full-Text | Cyber-Attack Scoring Model Based on the Offensive Cybersecurity Framework
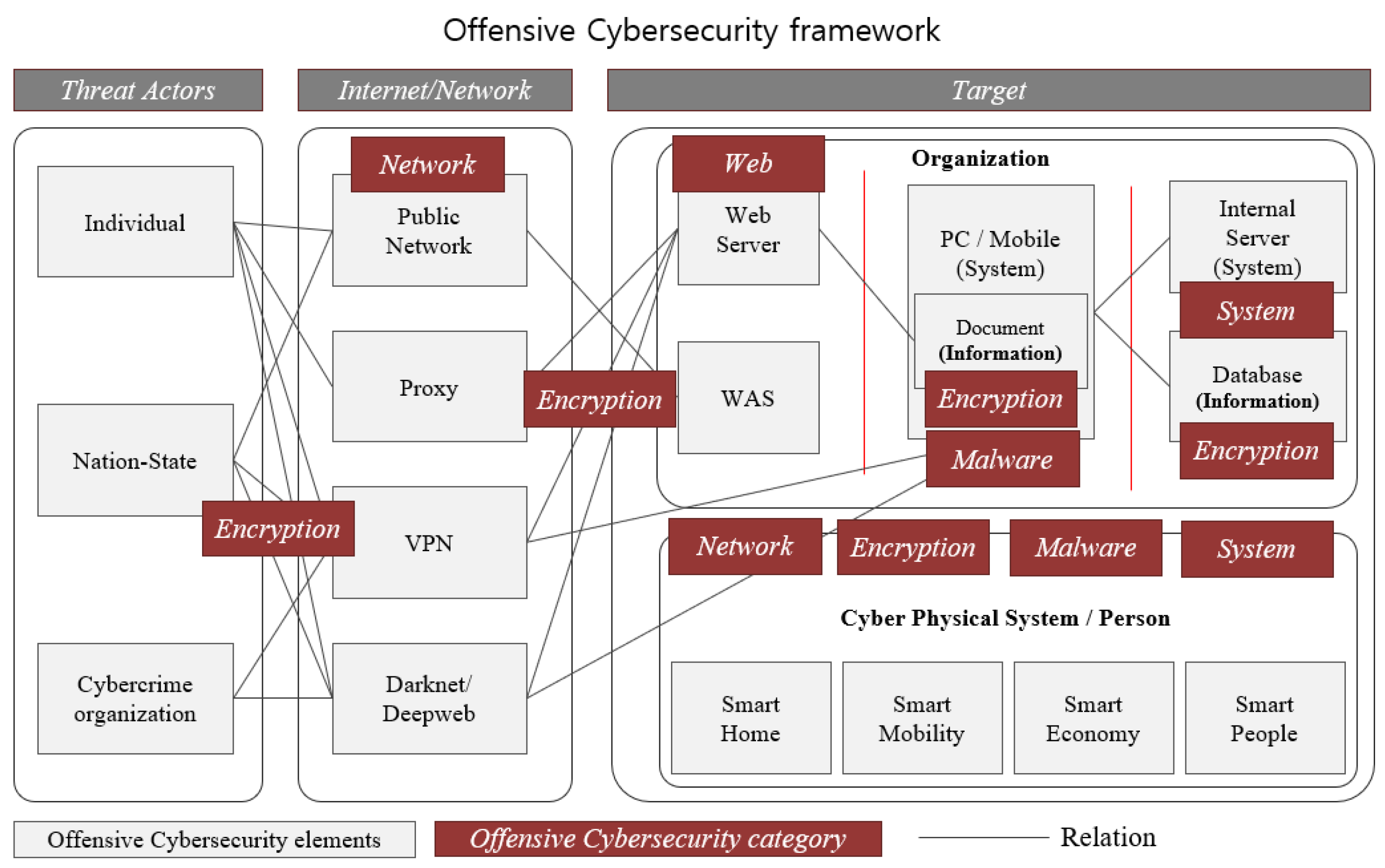
Applied Sciences | Free Full-Text | Cyber-Attack Scoring Model Based on the Offensive Cybersecurity Framework
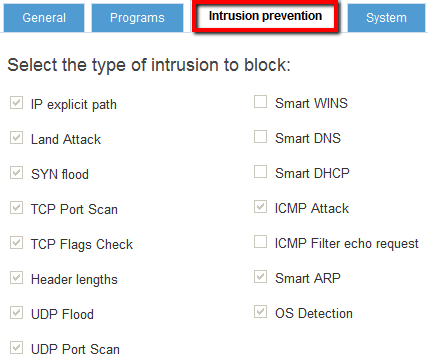
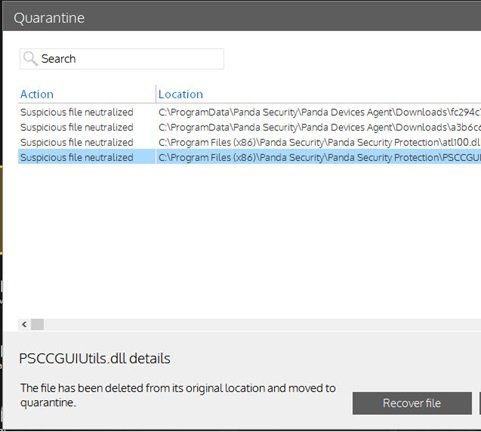
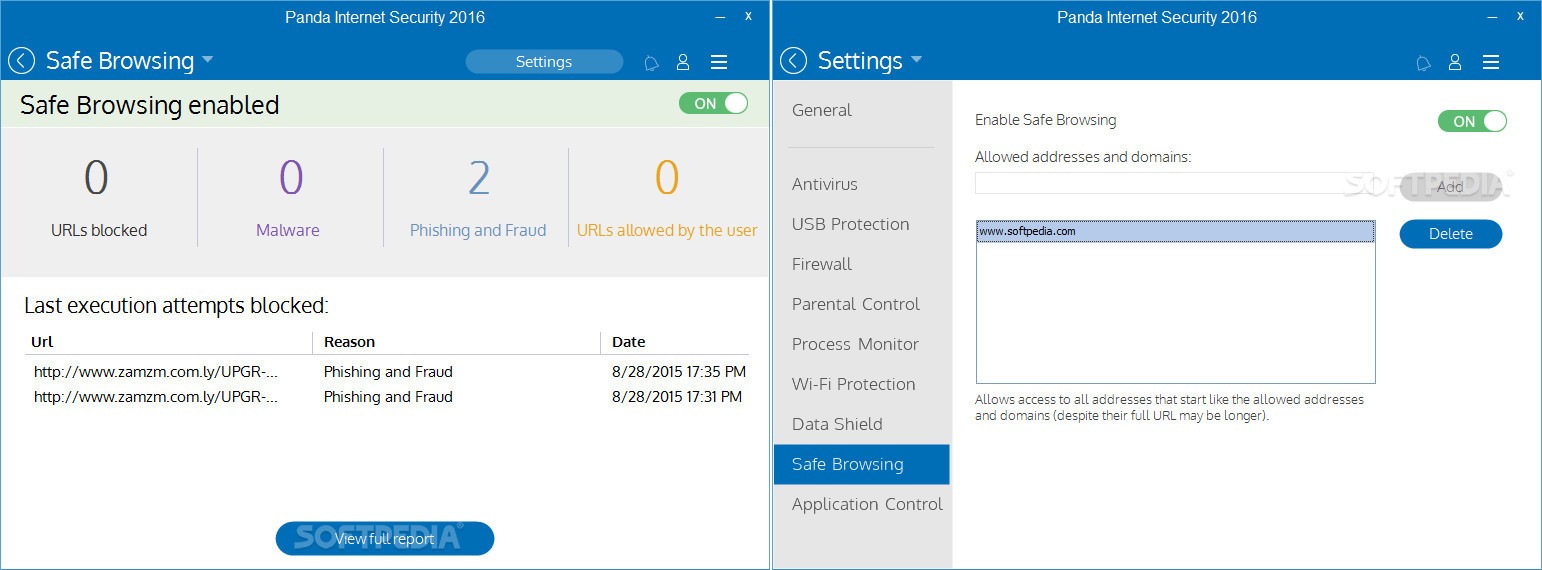
How is the firewall configured from the Endpoint Protection administration console? - Technical Support - Panda Security



![CLOSED] Invasion - Panda Security Forum CLOSED] Invasion - Panda Security Forum](http://www.pandasecurity.com/resources/img/sop/faqs/2014/41336-wifisettings.png)